Member-only story
Archangel | LFI to RFI, Crontab Exploitation and PATH Manipulation
Greetings everyone, hope you are well. Today I had the opportunity to analyze Archangel, başmelek in Turkish from TryHackMe platform.
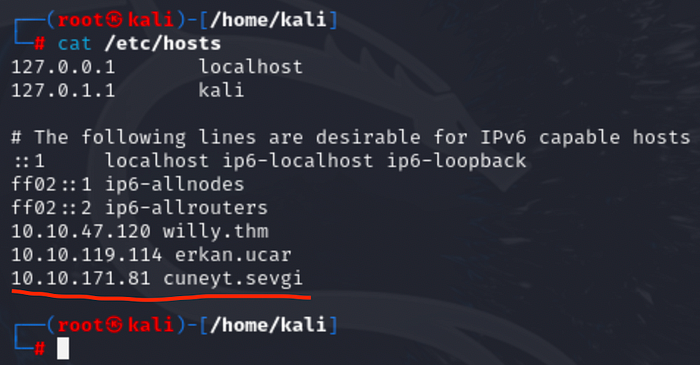
Add your ip address to hosts file to make customizable domain. This is a local method to override DNS resolution and create your own domain mappings for testing, development, or other purposes.
Run commands respectively
nano /etc/hosts<ipv4 address> <customized domain name>Control S and X
Final Result:
Reconnaissance
The faster you conduct reconnaissance, the more time you gain for the vulnerability detection and exploitation phases. Cyber intelligence is always a significant asset in understanding the technology an application uses and its vulnerability scope.
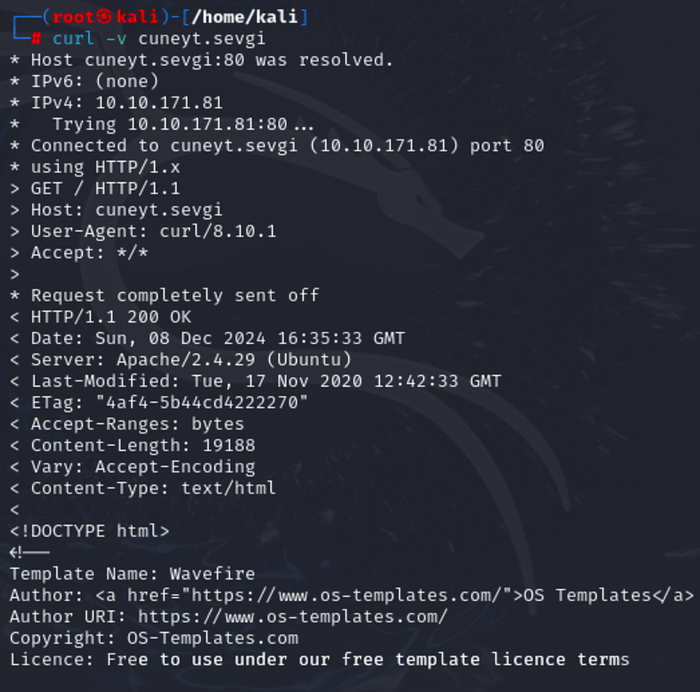
As penetration testers, we frequently seek to move directly to the vulnerability exploitation phase, but we should first gather information about the target, whether it involves application testing or local area network assessments. That’s why I conducted a curl scan to identify HTTP ports 80, 443, and Apache 8080. If further investigation is required, we should also perform a full-port scan. The technique I usually use is a demand-based approach, meaning we apply what is necessary based on the situation.
Let’s use curl:
curl -v cuneyt.sevgi
By default it will automatically move forward to port 80
There is nothing on other ports 443 and 8080:

Port 80 successfully identified web page's html structure and prompted as terminal output. Let me first analyze the source code's comment part and manually investigate with browser.
I saw an email address with domain @mafialive.thm as an internal information.

